Introduction
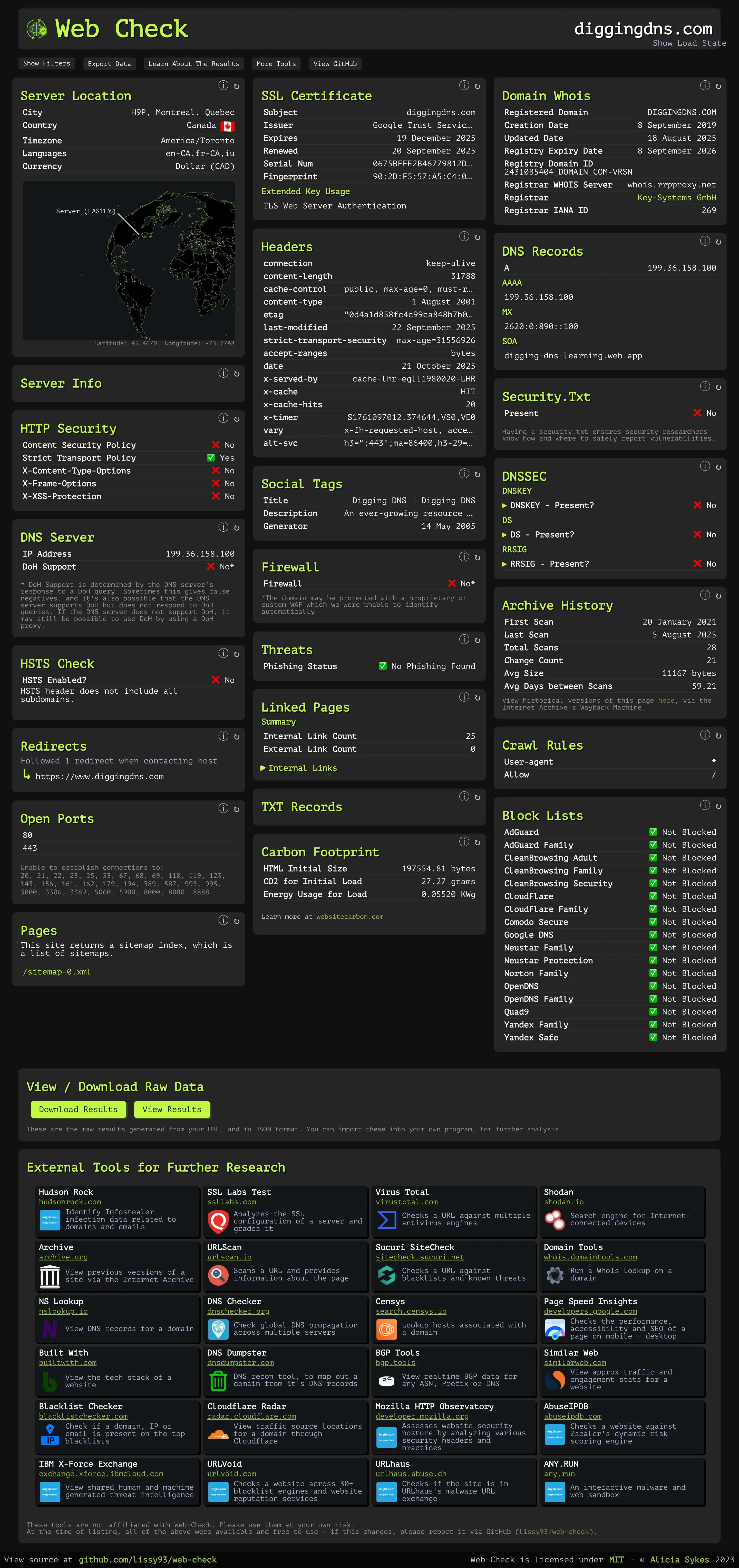
Web Check, available at https://web-check.xyz, is a fantastic online tool that performs over 30 different lookups against a target URL in a single click. It aggregates everything from IP details and DNS records to headers, certificates, and technology stacks, and provides quick links to dozens of other resources, all in an easy-to-read format. This makes it a nearly perfect launchpad for starting an investigation into a website.
Plus, it ticks a lot of boxes for the savvy investigator: it’s open source, easily self-hosted using Docker, and has an API. Seriously, what more could you want from a free resource?
The only minor drawback is its focus: it’s billed and built primarily as a website security assessment tool, not strictly a domain lookup tool. Therefore, it requires a full URL (including http:// or https://) to start a scan; you cannot just input a bare domain name.
For this article, I am only going to focus on using the public website version of the tool.
REMINDER: Use Third-Party Tools Cautiously Remember that when you use a public, third-party tool like this, the service operator (and potentially others) can see what you are querying. If operational security is a concern, take appropriate steps like using a VPN or Tor. Since Web Check is open source, you can mitigate this risk by running the tool locally on your own machine. However, keep in mind that even when self-hosted, the tool performs lookups against various external services and potentially the target itself, which could still expose your activity if not properly configured.
 (Screenshot showing the Web Check interface)
(Screenshot showing the Web Check interface)
How to Use It
Usage is straightforward. Visit https://web-check.xyz, enter the full URL you want to investigate (e.g., https://www.diggingdns.com) into the input box at the top, and click the Analyze button.
How It Works
When you initiate a query, Web Check performs dozens of checks in parallel. It queries public databases for WHOIS and DNS information, makes direct connections to the target server to analyze headers and TLS configurations, uses third-party APIs for reputation checks, and inspects the website’s code for technologies and links.
Reading the Results
At the time of writing, Web Check provides results across nearly 40 different categories. Here’s a breakdown of some of the most useful ones for OSINT investigators:
| Lookup | What It Means | How an OSINT Investigator Can Use It |
|---|---|---|
| IP Info | Geographical and network (ASN) information about the server’s IP address. | Identify hosting provider, ISP, country location. Pivot point for reverse IP lookups to find co-hosted domains. Assess if location matches expected business presence. |
| SSL Chain | Details of the site’s TLS/SSL certificate: subject (issued to), issuer (CA), validity period, SANs. | Confirm domain ownership/identity (for OV/EV certs). Subject Alternative Names (SANs) often reveal related subdomains. Validity period can hint at site longevity. |
| DNS Records | Key DNS records (A, AAAA, MX, NS, SOA, TXT) associated with the domain. | Identify hosting IP (A/AAAA), mail provider (MX), DNS host (NS). TXT records reveal SPF, verification tokens (linking to services like Google Workspace). SOA provides admin contact clues. |
| Cookies | Small data pieces stored by the browser, used for sessions, tracking, etc. | Reveal use of third-party analytics (Google Analytics), ad networks, specific web frameworks (e.g., session cookies). Map external dependencies and tracking methods. |
Crawl Rules (robots.txt) | Instructions for web crawlers specifying allowed/disallowed paths. | Disallow entries can reveal hidden admin panels, API endpoints, or directories not meant for public indexing but potentially accessible. |
| Headers | HTTP headers exchanged between browser and server (e.g., Server, Content-Type, Set-Cookie, X-Powered-By). | Fingerprint server software (Apache, Nginx), backend languages (PHP, ASP.NET), caching services (Cloudflare). Identify security headers (CSP, HSTS). Find content modification dates. |
| Server Location | Physical or network location estimate of the web server. | Corroborate or dispute claims about an organization’s location. Identify infrastructure geography. |
| Associated Hosts | Other hostnames/domains found linked to the target (shared IPs, analytics codes, SSL certs). | Crucial Pivot Point. Discover other websites/services operated by the same entity. Expand investigation scope from one site to a network. |
| Redirect Chain | Sequence of HTTP redirects from the initial URL to the final page. | Uncover affiliate links, tracking parameters, or malicious redirections. Understand the user journey and potential obfuscation techniques. |
| TXT Records | Arbitrary text stored in DNS, often for verification or email security (SPF, DKIM, DMARC). | Confirm use of specific services (Google, Microsoft 365). Reveal email infrastructure IPs/hostnames (SPF). Find other administrative metadata. |
| Server Status | HTTP status code returned (e.g., 200 OK, 404 Not Found, 503 Service Unavailable). | Confirm if site is live, down, or redirecting. Diagnose type of “down” (content missing vs. server error). Monitor for status changes over time. |
| Open Ports | Network ports open on the server (e.g., 80, 443, 22, 21). | Identify running services beyond web (SSH, FTP, mail, databases). Non-standard open ports can indicate misconfigurations or additional infrastructure. |
| Traceroute | Maps the network path (routers/hops) data takes to reach the server. | Reveal upstream network providers and geographic path. Identify potential points of network filtering or failure. |
| Server Info | Details about the server software (e.g., Apache/2.4.52, Nginx/1.21.0). | Fingerprint server technology and version. Check for known vulnerabilities associated with that software version. |
| Whois Lookup | Domain registration data (registrar, creation/expiration dates, status). | Establish domain age (indicator of legitimacy). Identify the registrar (for abuse reports). Note domain status codes (clientHold etc.). |
| Domain Info | More detailed registry info, including nameservers. | Nameservers are a strong pivot point for reverse NS lookups to find related domains. |
| Tech Stack | Breakdown of technologies used (languages, frameworks, CMS, libraries). | Detailed fingerprinting of the website’s build. Search for vulnerabilities in identified components (e.g., outdated WordPress plugins). Track actors using specific custom stacks. |
| Security.txt | Standardized file for security vulnerability reporting contacts. | Presence indicates security awareness. Provides direct contact points for responsible disclosure. Absence may suggest lower security maturity. |
| Linked Pages | Internal and external links found on the scanned page. | Discover site structure (internal links). Identify affiliations, partners, or external dependencies (external links). |
| Email Configuration | Analysis of MX, SPF, DKIM, DMARC records. | Reveal email provider. Assess vulnerability to email spoofing. Identify mail server IPs/hostnames for further investigation. |
| Firewall Detection (WAF) | Attempts to identify if a Web Application Firewall is protecting the site. | Assess target’s defenses. Presence of WAF (like Cloudflare, Akamai) can make direct server interaction difficult. |
| Archive History | Links to snapshots of the site on the Wayback Machine (Internet Archive). | View historical versions of the site. Find content, contact details, or infrastructure clues that have been removed from the live site. |
| Malware & Phishing Check | Checks URL against databases of known malicious sites (e.g., Google Safe Browsing). | Critical Finding. Immediately flags the site as dangerous. Strong indicator of malicious intent. |
| TLS Cipher Suites | Encryption algorithms offered by the server for TLS connections. | Can create a unique server fingerprint (JA3S/CYU hash) to track the same configuration across different IPs. |
At the bottom of the Web Check results page, you’ll find a curated list of External Links. This section provides about two dozen direct links to other useful OSINT tools where you can further investigate the target URL, domain, or IP address. These range from malware analyzers and IP reputation checkers to threat intelligence platforms and subdomain finders. If you have a particular angle you’re pursuing, these links offer a quick portal to deeper dives on specialized platforms.
Strengths
- All-in-One Convenience: Aggregates a massive amount of data from various sources into a single, easy-to-read dashboard, saving significant time.
- Open Source & Self-Hostable: Allows for privacy and customization if you run your own instance.
- Detailed Error Reporting: Often explains why a particular lookup failed and provides a retry button, which is great for troubleshooting.
- Exportable Data (JSON): Easily download the complete results in JSON format for offline analysis or integration with other tools.
- Free: Provides immense value with no ads, paywalls, or strict limits on the public site.
Limitations
- Requires a Full URL: Cannot perform lookups on just a domain name; needs
http://orhttps://. - No Historical Data (on public site): The results are a snapshot in time. For historical tracking, you’d need to self-host and implement your own data storage.
- Not All Lookups Equally Valuable: Some data points (like “Carbon Footprint” or basic “Quality Metrics”) might be less relevant for pure OSINT investigations.
- Occasional Tool Failures: As with any tool relying on multiple external sources, some lookups might occasionally fail or time out. Given that it’s free, this is a minor inconvenience.

